Security in Mining Pools: How to Protect Your Earnings
Security in mining pools is a critically important aspect that every miner must consider to protect their investments and maximize their profits. With the ever-growing threat of cyberattacks, ensuring security becomes a priority for all participants in the process. In this review, we will discuss in detail what security measures can and should be applied to protect your income in mining pools.
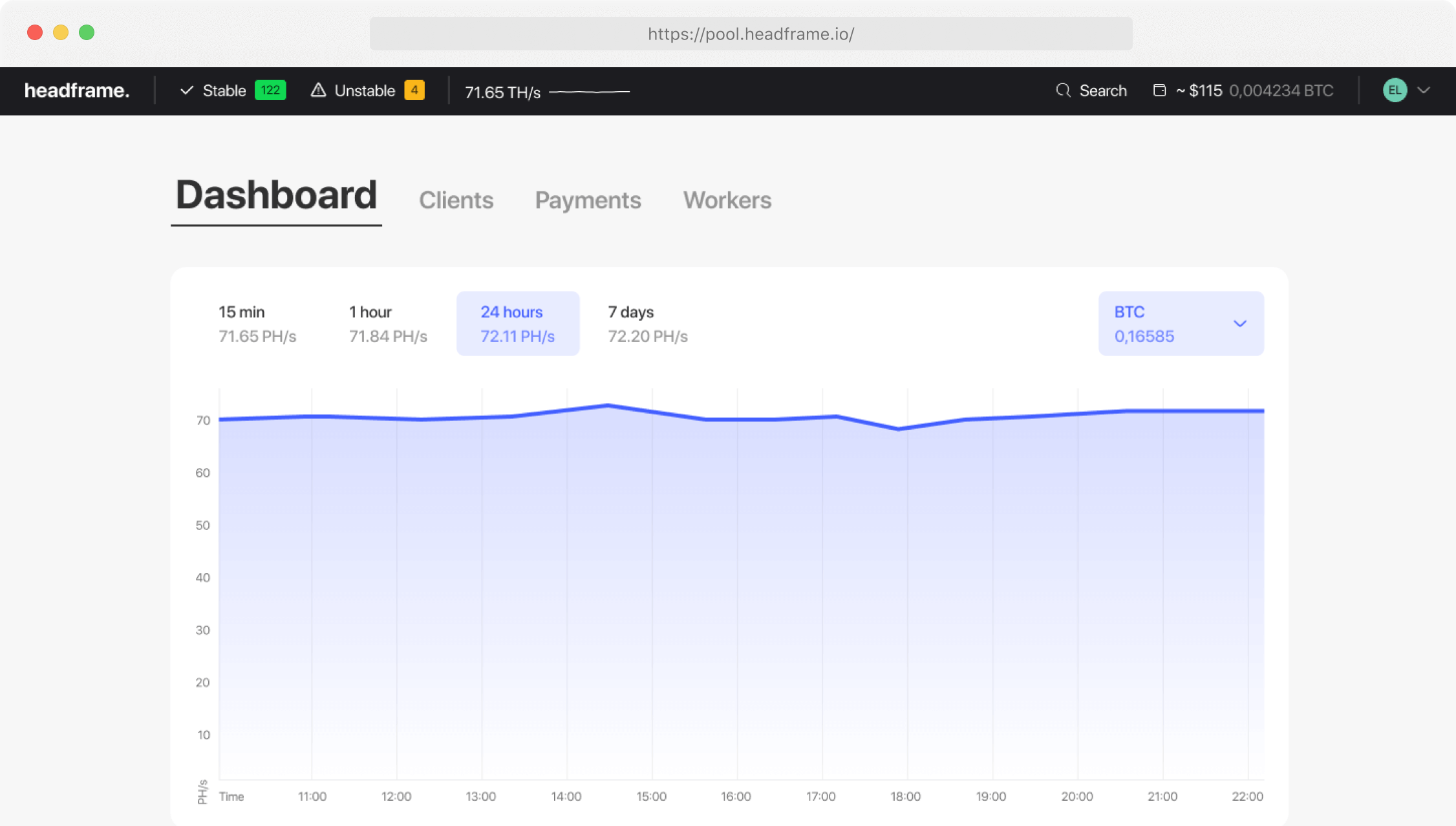
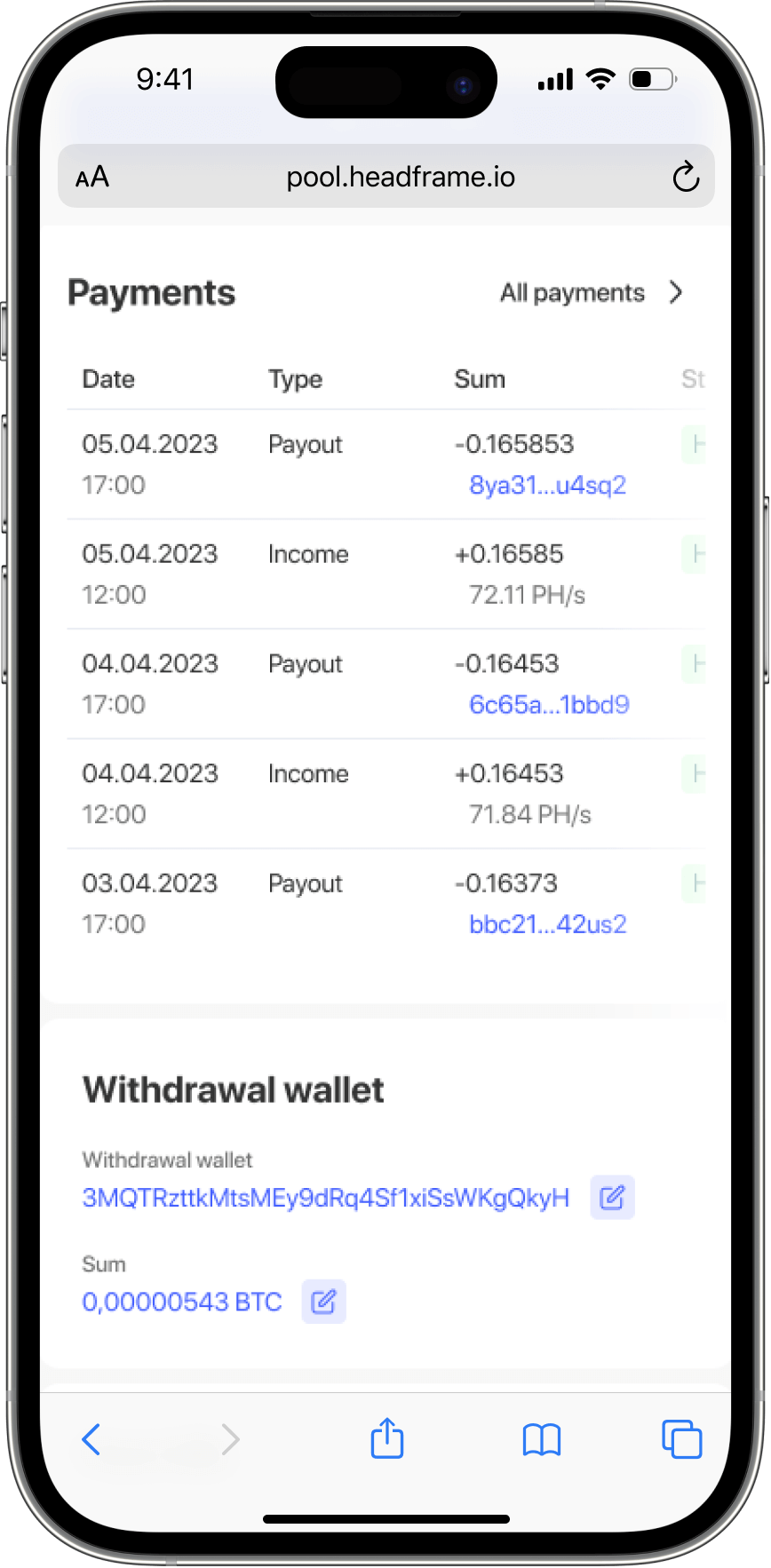
Earn more money with Headframe
Join a mining pool and get the best profitability in mining. Already more than 10,000 miners trust Headframe.
First and foremost, it is important to choose a reliable mining pool. The reliability of a pool can be assessed by several parameters, including its history in the industry, user reviews, and the transparency of its operations. Established mining pools are less prone to hacking risks and typically use advanced technologies to protect their clients’ data. Choosing such a pool reduces the likelihood of losing income due to cyberattacks or financial fraud.
Next, it is crucial to pay attention to the security measures offered by the pool itself. These include two-factor authentication, data encryption, and regular security audits. Two-factor authentication is a process that requires two different forms of identity verification before accessing the account, significantly reducing the risk of unauthorized access.
Data encryption protects sensitive information such as your wallet details and transactions from prying eyes. Regular security audits conducted by independent third parties can identify vulnerabilities in the pool’s security system before they are exploited by attackers.
Besides technical aspects, behavioral security measures must also be considered. For example, always be critical of any emails or messages requesting your personal data or offering dubious investment schemes. Phishing is a common method used by fraudsters to gain access to your accounts.
Additionally, regularly updating your software, including antivirus programs and mining software, helps protect your system from known vulnerabilities that can be exploited in an attack. Securing your local equipment is also crucial, as compromised or infected devices can jeopardize your mining operations and even lead to loss of income.
A backup and data recovery strategy should also be considered. Having a reliable backup plan can prevent the loss of important information in case of an attack or equipment failure. This includes not only backing up wallets and keys but also the entire system configuration and mining software settings.
It is important to note that mining security in a pool is not limited to technical aspects alone. Legal aspects also play an important role. Depending on your jurisdiction, there may be certain rules and regulations regarding cryptocurrency mining that need to be followed to avoid legal issues. Understanding and complying with these laws helps protect you not only from legal threats but also from potential fines or other sanctions.
Financial planning and risk management are also critical for protecting your income. This includes sensible capital management, investment diversification, and preparation for possible market fluctuations. In the world of cryptocurrencies, where prices can fluctuate greatly, it is important to have a clear understanding of your financial goals and the level of risk you are willing to take.
Finally, participating in the mining pool community and actively communicating with other miners can provide additional insights and tips for enhancing security. Many pools have forums or chats where participants share experiences and information about new threats, protection methods, and best practices. Such communication not only strengthens the security of your mining process but also helps create a support network that can be invaluable if problems arise.
Ultimately, protecting your income in mining pools requires a comprehensive approach that includes technical, legal, and financial aspects, as well as active community participation. Being informed and prepared for various risks significantly increases your chances of successful and secure mining.