Which New Mining Algorithms Are Preferred by Modern Pools?
Modern mining pools play an important role in the cryptocurrency ecosystem, combining the computing power of many participants for more efficient cryptocurrency mining. In the context of rapidly evolving technologies and increasing demands for security and energy efficiency, mining pools are actively adopting new mining algorithms. Let’s explore which algorithms are preferred by modern mining pools and how they help improve the efficiency and security of mining operations.
Earn more money with Headframe
Join a mining pool and get the best profitability in mining. Already more than 10,000 miners trust Headframe.
Proof of Stake (PoS)
One of the most popular new algorithms used by mining pools is the Proof of Stake (PoS) algorithm. Unlike the traditional Proof of Work (PoW) algorithm, which requires significant computing power and energy, PoS is based on the amount of cryptocurrency held by a user. Participants with more coins have a higher chance of confirming transactions and receiving rewards. This approach significantly reduces energy consumption and improves the ecological sustainability of mining. Mining pools using PoS attract miners looking for more energy-efficient and sustainable solutions.
Delegated Proof of Stake (DPoS)
Another algorithm gaining popularity among modern mining pools is Delegated Proof of Stake (DPoS). This algorithm is a modification of PoS and uses delegates to confirm transactions. Network participants elect delegates responsible for validating blocks and maintaining network security. This approach achieves high performance and scalability, making it attractive to mining pools handling large transaction volumes. DPoS also provides more democratic network governance, enhancing trust among participants.
Proof of Space (PoSpace) and Proof of Time (PoT)
Algorithms based on Proof of Space (PoSpace) and Proof of Time (PoT) are also finding applications in modern mining pools. These algorithms use free disk space and time to confirm transactions. PoSpace requires participants to provide free disk space for data storage, reducing the need for powerful computing resources. PoT is based on the time spent performing specific tasks, also contributing to reduced energy consumption. These algorithms offer new opportunities for miners seeking alternatives to traditional approaches.
Hybrid Algorithms
Mining pools are also actively exploring and implementing hybrid algorithms that combine elements of various methods. Hybrid algorithms allow leveraging the advantages of several approaches to achieve optimal performance and security. For example, combining PoW and PoS can provide high security and decentralization while improving energy efficiency. Hybrid solutions help mining pools adapt to changes in the technological environment and meet growing user demands.
Security
Security remains a key factor in choosing mining algorithms. Modern mining pools actively implement algorithms that provide high protection levels against attacks, such as 51% attacks. Algorithms using multi-factor authentication and data encryption help prevent unauthorized access and protect participants’ assets. Implementing advanced security methods allows mining pools to strengthen trust among participants and safeguard their assets from potential threats. This is particularly important in the context of increasing competition and the intensification of attacks by malicious actors.
ASIC-Resistant Algorithms
Additionally, some mining pools prefer algorithms resistant to ASIC devices. ASIC-resistant algorithms, such as Equihash or RandomX, require the use of more diverse and standard equipment, such as GPUs or CPUs, helping maintain a more even distribution of computing power and network decentralization. This prevents mining monopolization by large players and promotes fairer reward distribution.
Continuous Updates and Infrastructure
Adapting to new algorithms also requires mining pools to continuously update their software and infrastructure. Using modern technologies such as cloud solutions and distributed systems improves the pool’s scalability and resilience. This is important for ensuring high performance and reliability of mining operations, especially with the increasing number of users and transactions.
Support for Innovative Projects
Another important aspect is supporting innovative projects and startups developing new mining algorithms and technologies. Mining pools can invest in such projects or collaborate with them to be the first to implement advanced solutions and remain competitive. This contributes not only to the development of the pools themselves but also to the entire cryptocurrency ecosystem, stimulating innovations and improving the technological base.
User Experience
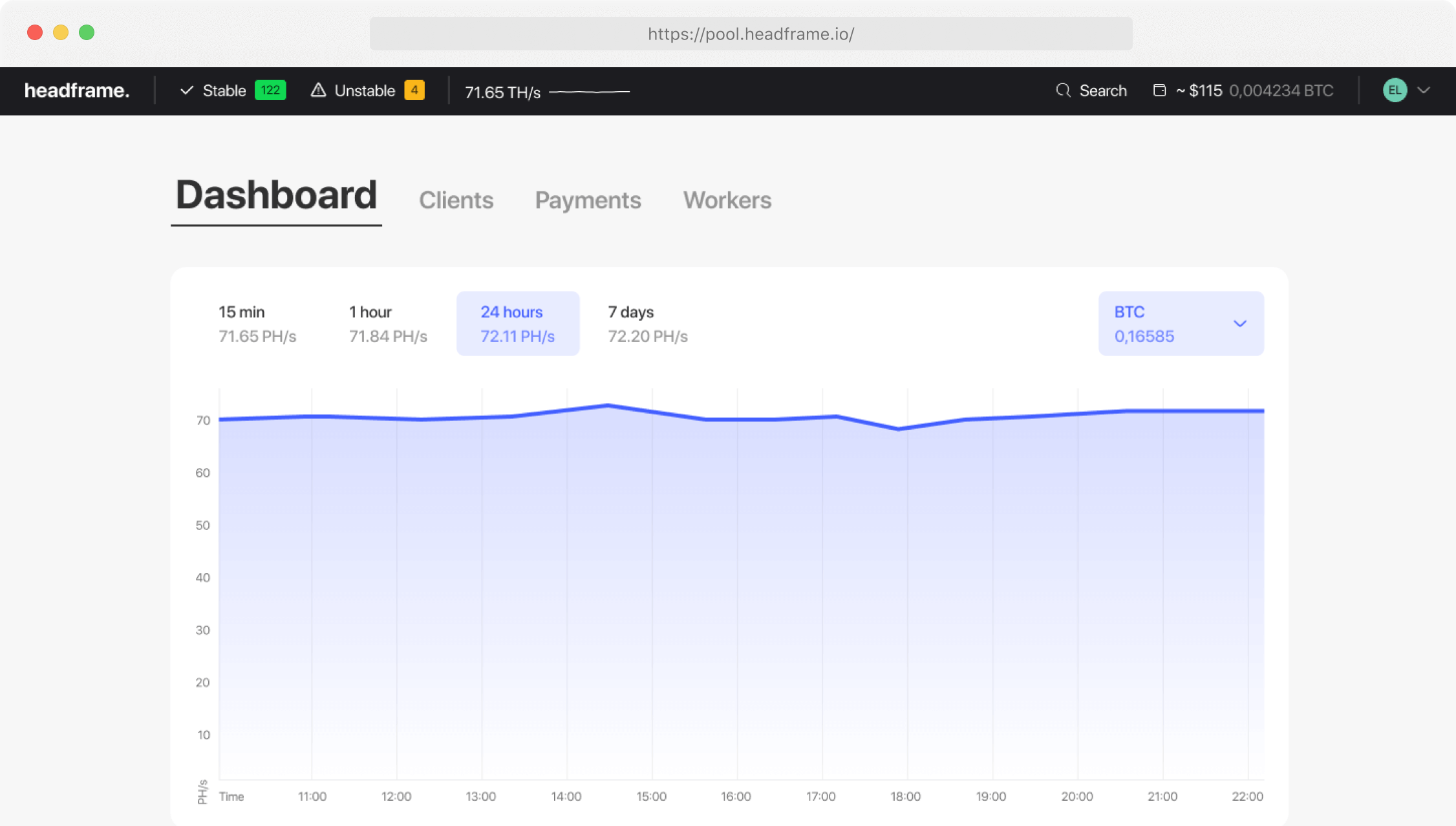
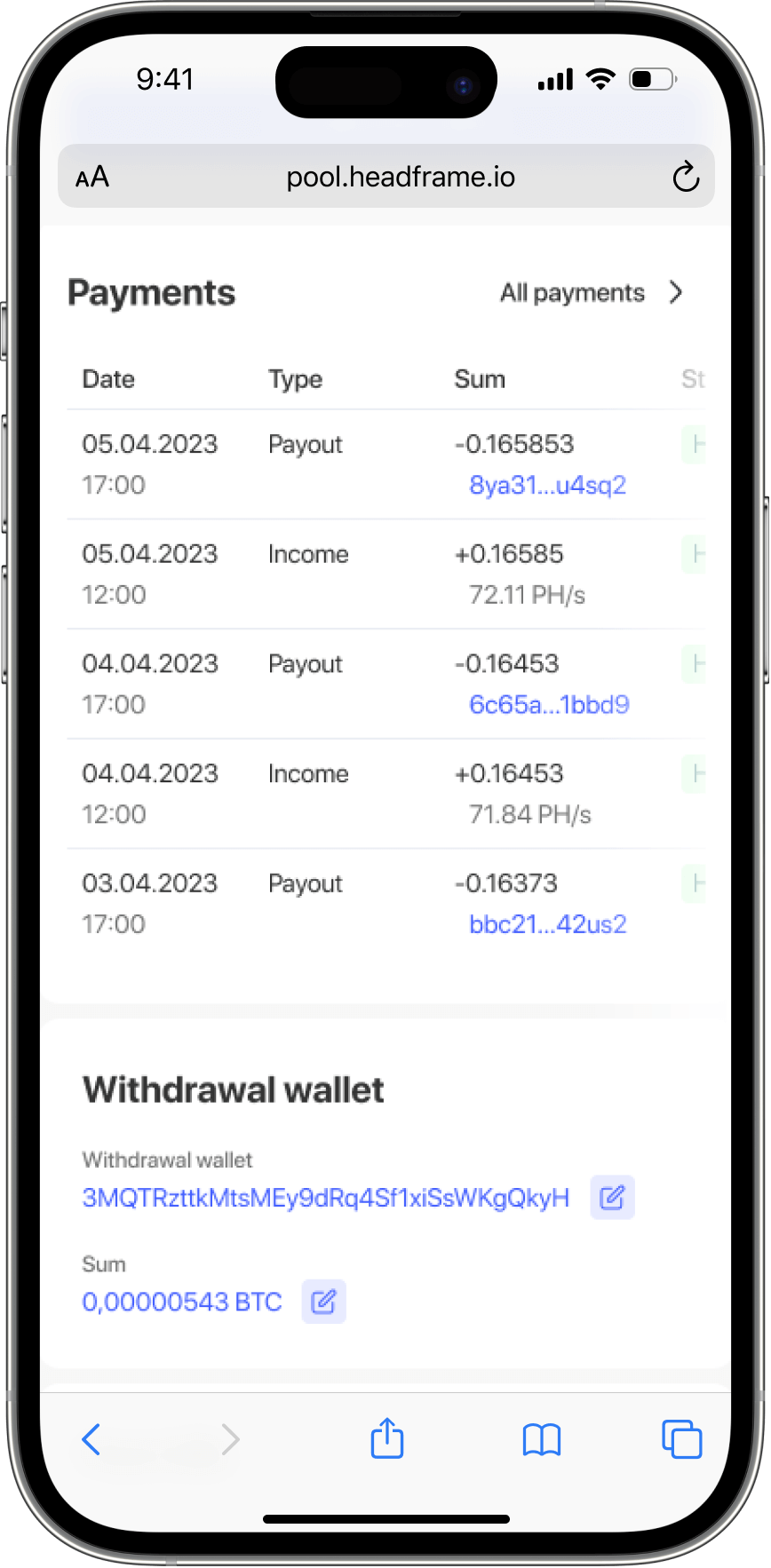
User experience also plays a crucial role in choosing mining algorithms. Mining pools offering user-friendly interfaces and quality support attract more users. This includes not only technical support but also educational resources that help miners better understand and use new algorithms. Educating users on new technologies and mining methods promotes their successful adaptation and increased income.
Thus, modern mining pools actively implement and use various mining algorithms to enhance the efficiency, security, and sustainability of their operations. Algorithms such as Proof of Stake, Delegated Proof of Stake, Proof of Space and Time, as well as hybrid solutions and ASIC-resistant methods, play an important role in this process. Implementing these algorithms helps mining pools adapt to changing market conditions, improve user experience, and promote the sustainable development of the cryptocurrency ecosystem. Understanding and applying these strategies allow mining pools to remain at the forefront of the industry and ensure stable incomes for their participants.