Best Security Practices for Mining Pool Participants
Security is one of the most important parts of participating in a mining pool. Because mining involves accounts, wallets, software, and ongoing network connectivity, even simple mistakes can lead to stolen funds, compromised systems, or broader operational risk.
A strong security approach depends on both technical protection and everyday user discipline.
Use strong account protection
Mining pool accounts should always use strong, unique passwords rather than credentials reused from other platforms. Two-factor authentication adds another important layer by making unauthorized access more difficult even if a password is exposed.
Account protection is the first line of defense because compromised credentials are still one of the easiest ways attackers gain access.
Keep software updated
Mining software, operating systems, drivers, and supporting applications should be updated regularly. Security updates help close vulnerabilities that attackers may use to install malware or hijack a system.
Even if the mining setup seems stable, outdated software can quietly become a serious risk.
Watch for phishing and suspicious links
Phishing remains one of the most common threats in the crypto space. Attackers may use fake pool logins, deceptive emails, or social messages to steal credentials or wallet details. Participants should be careful with links, attachments, and unexpected account-related messages.
If a message seems urgent or unusual, it is worth verifying it independently before taking any action.
Use antivirus and anti-malware protection
Reliable security software helps detect malicious files and suspicious behavior before more damage occurs. Antivirus and anti-malware tools should be kept current so they can respond to newly emerging threats.
These tools do not replace good habits, but they are an important part of layered protection.
Protect the network connection
A secure network environment reduces the chance of external interference. Firewalls, traffic filtering, and strong router settings all help control what reaches the mining system. If participants access mining services through remote or public networks, using an encrypted VPN connection can add useful protection.
Network security matters because mining devices are often online continuously.
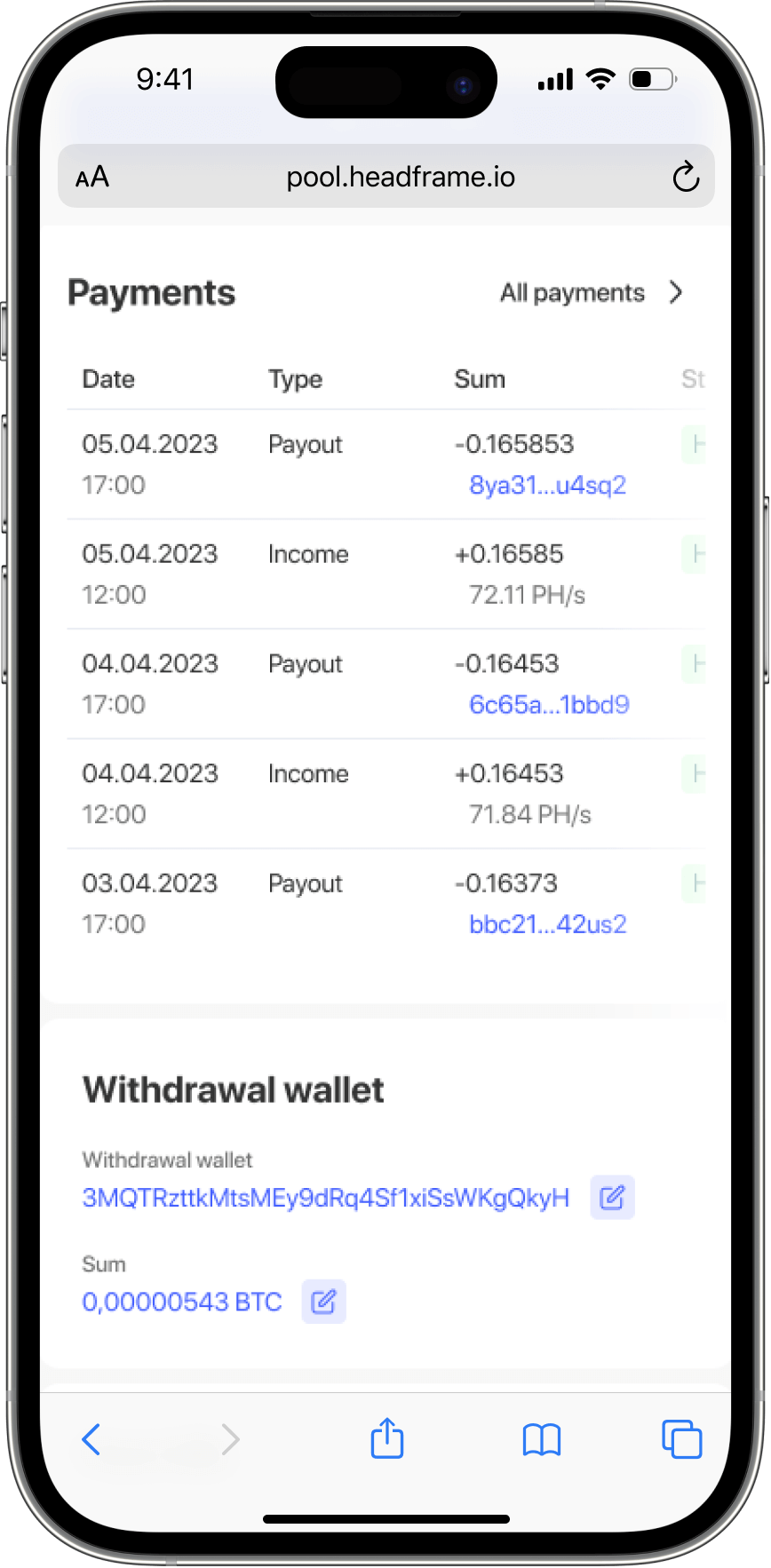
Secure wallet management
Wallet protection is essential because mining rewards eventually accumulate somewhere. It is safer not to keep all funds in one location, especially for long-term storage. Hardware wallets or other strong-storage options are generally better suited to protecting larger balances than leaving everything in hot wallets or exchange accounts.
Regular backups are also necessary in case devices fail or credentials are lost.
Be aware of social engineering
Not every attack targets software directly. Some attackers rely on social engineering, using impersonation, pressure, or fake support contacts to obtain sensitive information. Staying aware of these tactics helps prevent mistakes that no firewall can stop.
Education and skepticism are both practical security tools in this context.
Conclusion
Good mining pool security is built from a combination of strong passwords, two-factor authentication, updated software, careful wallet management, safe browsing habits, and secure network use. No single step is enough by itself, but together they reduce risk significantly.
Participants who treat security as an ongoing practice rather than a one-time setup are much better positioned to protect their funds and systems over the long term.