Best Security Practices for Mining Pool Participants
Security always comes first, especially when it comes to cryptocurrency mining. Participants in mining pools must be aware of potential threats and know how to protect themselves and their resources. In this context, knowing and applying best security practices becomes critically important to ensure the reliability and stability of both individual mining operations and the entire mining pool.
Earn more money with Headframe
Join a mining pool and get the best profitability in mining. Already more than 10,000 miners trust Headframe.
The importance of cybersecurity in mining cannot be underestimated. Miners, like any other internet users, are at risk of phishing attacks, malware, and other forms of cyber threats. However, in the context of mining pools, the consequences of such attacks can be particularly devastating, as they can lead to the loss of significant amounts of cryptocurrency and even compromise the entire pool.
One of the primary precautions for mining pool participants is to use strong and unique passwords for all their accounts, as well as enabling two-factor authentication (2FA) wherever possible. These measures can significantly hinder unauthorized access to accounts, even if the username and password become known to attackers.
Mining pool participants should also pay special attention to the security of their software. Regularly updating the operating system and all applications, including mining software, helps protect computers from vulnerabilities that could be exploited by attackers to hack or infect with malware.
Besides technical measures, it is crucial to exercise caution when handling emails and links. Phishing is a common method by which scammers attempt to steal personal data. Miners must be particularly careful not to click on suspicious links or open attachments in emails from unknown senders.
Investing in good antivirus and anti-malware software is also a key aspect of security. Ensuring that your system is protected from the latest threats can help prevent many cyberattack attempts. The software should be continuously updated to effectively deal with new malware and exploits.
Network protection is another critically important element for mining pool participants. Using a reliable firewall and network filters can help monitor and control incoming and outgoing traffic, preventing unauthorized access to network resources. It is also important to consider using encrypted VPN connections when accessing the mining pool from remote or public networks to protect traffic from interception.
Privacy and anonymity can also play a significant role in the security of mining pool participants. Using anonymizing services and technologies like Tor or VPN can help hide participants’ identities and locations, which is especially important in countries with strict cryptocurrency regulations.
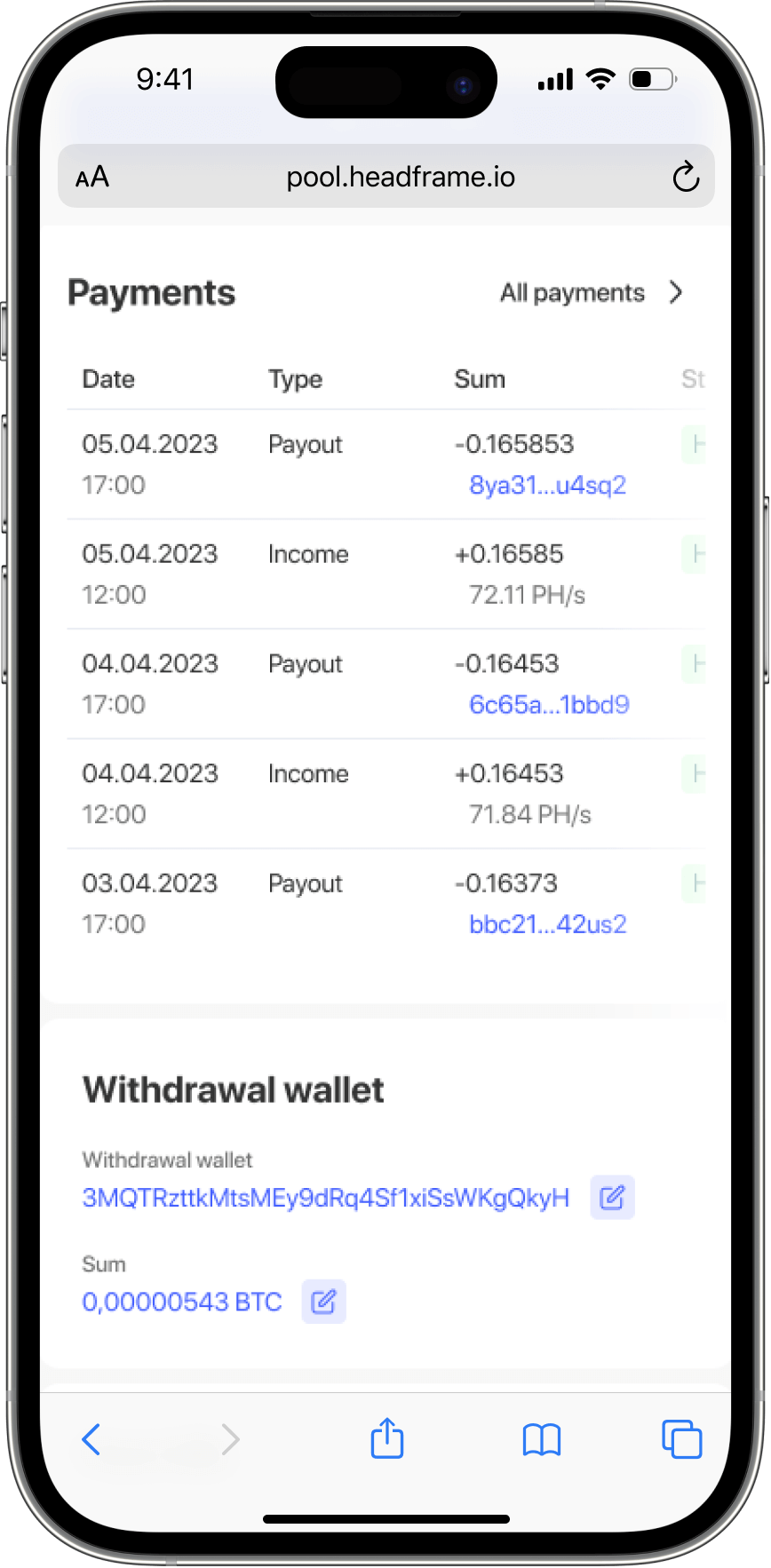
Managing cryptocurrency wallets is another aspect of security. It is important to use reliable wallets that offer multi-level protection and backup options. Participants should avoid storing all their funds in one place and consider using hardware wallets for long-term storage of large amounts.
Finally, mining pool participants should be aware of social engineering and other manipulation techniques that attackers may use to obtain confidential information. Education and constant awareness of the latest fraud methods will help participants protect themselves from potential attacks.
Overall, security in mining pools is a complex task requiring a comprehensive approach and constant attention. By following these best practices, mining pool participants can significantly reduce their risks and ensure the security of their assets and data.